Building an internal SOC team
with Tier 1 analysts to provide
24x7 coverage.
Expanding AI features
from their existing
SIEM provider.
Trialing other AI SOC vendors
promised efficiency,
delivered less.
AiStrike stood out because it went far beyond AI-assisted triage. It delivered end-to-end SOC automation in a single SaaS platform — spanning detection, investigation, response, and proactive threat hunting.
.avif)
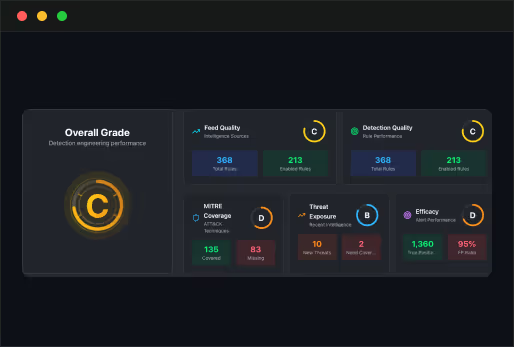
Comprehensive SOC Fabric
Automation that covers the entire SOC lifecycle: detection engineering, investigation, response, and threat hunting.
.png)
Built-in SOAR + Case Management
A unified system of record, eliminating the need for separate tools.
.png)
Human-in-the-Loop Learning
Continuous improvement as AiStrike tunes detections and investigations with analyst feedback.
.png)
Threat Exposure Analysis
Intelligence from 100+ sources (Mandiant, Unit 42, Verizon DBIR, and more) drives proactive detections against emerging threats.
.avif)
Agentless SaaS Deployment
Fast, seamless onboarding; operational in just two weeks without heavy infrastructure or agents.
“ When we relied on MDR, most of our time was spent chasing false positives and justifying costs. With AiStrike, that changed almost immediately. Every alert is now investigated, and instead of hundreds of escalations, we only see the handful that truly matter. We’ve cut costs in half, improved coverage, and gained a single place to investigate and respond. For the first time, our SOC feels efficient, proactive, and future-ready. ”

Varun Singhal
Director of Information Security, Sunrun
50%+ Cost Reduction
Lower spend compared to the MDR provider, while delivering broader coverage.
80% Fewer Escalations
Noise dropped dramatically, enabling analysts to focus on actionable incidents.
MTTA Under 30 Minutes
Automated case creation and Slack/email notifications cut acknowledgment times from hours to minutes.
Improved Detection Fidelity
New detections created for unmonitored log sources, closing critical gaps.
Consolidated Reporting & Compliance
Built-in case management and NotebookLM integration gave Sunrun visibility into MTTA, MTTR, and
compliance gaps.
Rapid Time-to-Value
From contract to fully operational in two weeks.
Close Collaboration
AiStrike worked side by side with Sunrun’s team to fine-tune integrations and workflows.
Responsive Support
Quick to adapt, address feedback, and add new enhancements.
Visionary Roadmap
A clear direction for advancing SOC automation, including proactive detection optimization and
exposure analysis.













.svg)

.svg)
.avif)
.avif)


.avif)
.avif)
.avif)
.svg)
.svg)
.svg)
.svg)
.svg)
.svg)

.avif)
.avif)


.png)
.png)

.png)

.png)
.webp)
.webp)
.png)
.png)


.png)
.png)
.png)

.svg)


.avif)
.avif)
.png)
.png)
.png)
.avif)
